Your Software token vs hardware token images are available in this site. Software token vs hardware token are a topic that is being searched for and liked by netizens now. You can Find and Download the Software token vs hardware token files here. Get all royalty-free vectors.
If you’re searching for software token vs hardware token pictures information connected with to the software token vs hardware token interest, you have visit the ideal site. Our website always provides you with hints for viewing the highest quality video and image content, please kindly surf and find more informative video articles and graphics that fit your interests.
Software Token Vs Hardware Token. Authentication into the web platform is also done via usernamepassword but transactions are performed by authenticating into a software token. When I was checking them the vendor listed the SKUs with battery life listed in years. A software token is a virtual piece of software that is installed on a users electronic device such as a mobile phone. Authentication tokens that are not physically tangible but exist as software on common devices for example computers or phones.
 Hardware Or Software Token Which One To Choose Protectimus From protectimus.com
Hardware Or Software Token Which One To Choose Protectimus From protectimus.com
The software tokens can be installed on a users desktop system in the cellular phone or on the smart phone. Buy supported hardware tokens from WatchGuard or a third-party vendor. Hardware tokens are popular for IT admins that want to have a more physical management of keys. When I was checking them the vendor listed the SKUs with battery life listed in years. For example you cant lose a software-based token feed it to the dog or put it through the wash. You can purchase WatchGuard hardware tokens or you can use third-party hardware tokens with AuthPoint.
Authentication into the web platform is also done via usernamepassword but transactions are performed by authenticating into a software token.
A software token is a virtual piece of software that is installed on a users electronic device such as a mobile phone. There is no sense to dispute this fact but it must be kept in mind that it is worth it. Software tokens are software that generate tokens for you. There are three basic categories of hardware authentication tokens on the marketvisual tokens which display a code to be entered touch or plug-in tokens which enter codes or credentials themselves via USB and wireless tokens which enter codes or credentials over the air using near-field communication NFC or low energy Bluetooth BLE. Hardware tokens are physical devices dedicated to being an authentication token. Then view the tokens for each processor definition in the production IODFs until you find the IODF with the token that matches the token in HSA.
 Source: doubleoctopus.com
Source: doubleoctopus.com
Hardware tokens are popular for IT admins that want to have a more physical management of keys. In addition please read the Important Statement from RSA Regarding RSA SecurID Software Token Provisioning Best Practices. Option hardware token. Authentication into the web platform is also done via usernamepassword but transactions are performed by authenticating into a software token. There are hardware MFA such as RSA tokens that generate codes.
 Source: pinterest.com
Source: pinterest.com
A software token is a virtual version of a token accessible through another device such as a smartphone. Token based authentication systems are stronger more secure because they require two-factor authentication. You can purchase WatchGuard hardware tokens or you can use third-party hardware tokens with AuthPoint. They are only available in increments of 10. A token is a device that employs an encrypted key for which the encryption algorithmthe method of generating an encrypted passwordis known to a networks authentication server.

Hard Tokens Have Done Their Bit. The software tokens can be installed on a users desktop system in the cellular phone or on the smart phone. Authentication into the web platform is also done via usernamepassword but transactions are performed by authenticating into a software token. You can purchase WatchGuard hardware tokens or you can use third-party hardware tokens with AuthPoint. A token is a device that employs an encrypted key for which the encryption algorithmthe method of generating an encrypted passwordis known to a networks authentication server.
 Source: sciencedirect.com
Source: sciencedirect.com
Token based authentication systems are stronger more secure because they require two-factor authentication. Bypass codes are generated by an administrator and distributed to a user to bypass their second factor eg. The software tokens can be installed on a users desktop system in the cellular phone or on the smart phone. Import hardware tokens to AuthPoint. They are only available in increments of 10.
 Source: pinterest.com
Source: pinterest.com
To do so you must. Then view the tokens for each processor definition in the production IODFs until you find the IODF with the token that matches the token in HSA. A software token is a virtual version of a token accessible through another device such as a smartphone. The factors in a token based system are something the user knows a PIN and something a user has the token. They offer a more flexible dynamic secure and easy-to-manage option in todays increasingly mobile and cloud-based environments.
 Source: sciencedirect.com
Source: sciencedirect.com
You may have also heard hard tokens called key fobs security tokens or USB tokens among other names. For example the Google Authenticator App or Authy on your smartphone while hardware tokens are actual hardware that are only made for generating those tokens without doing anything else such as RSA SecurID. A hard token allows you to access software and verify your identity with a physical device rather than relying on authentication codes or passwords but still uses multiple factors in authorizing access to software. The software tokens can be installed on a users desktop system in the cellular phone or on the smart phone. Order Tokens Directly from Duo.
 Source: protectimus.com
Source: protectimus.com
There are three basic categories of hardware authentication tokens on the marketvisual tokens which display a code to be entered touch or plug-in tokens which enter codes or credentials themselves via USB and wireless tokens which enter codes or credentials over the air using near-field communication NFC or low energy Bluetooth BLE. Hard Tokens Have Done Their Bit. Tokens are used as one of the possible factors for authentication. A hardware token eToken. A hardware token is a physical device with a built-in token that your users can use for authentication.
 Source: infosecurity-magazine.com
Source: infosecurity-magazine.com
Then view the tokens for each processor definition in the production IODFs until you find the IODF with the token that matches the token in HSA. A hardware token eToken. There are hardware MFA such as RSA tokens that generate codes. For example you cant lose a software-based token feed it to the dog or put it through the wash. If a user forgets their phone or hardware token but still needs access.

SMS hardware token and Duo Mobile-generated passcodes are generated by the user and used to complete the second factor to authenticate to a protected application. There are three basic categories of hardware authentication tokens on the marketvisual tokens which display a code to be entered touch or plug-in tokens which enter codes or credentials themselves via USB and wireless tokens which enter codes or credentials over the air using near-field communication NFC or low energy Bluetooth BLE. It is directed to deployments of RSA SecurID software tokens but there is content applicable to hardware tokens as well. Hard tokens are physical objects used to grant access to a restricted digital asset. This solution is cost effective and can be rolled out broadly.
 Source: hideez.com
Source: hideez.com
Hardware tokens are physical devices dedicated to being an authentication token. A token is a device that employs an encrypted key for which the encryption algorithmthe method of generating an encrypted passwordis known to a networks authentication server. They have their pros and cons. SMS hardware token and Duo Mobile-generated passcodes are generated by the user and used to complete the second factor to authenticate to a protected application. Import hardware tokens to AuthPoint.
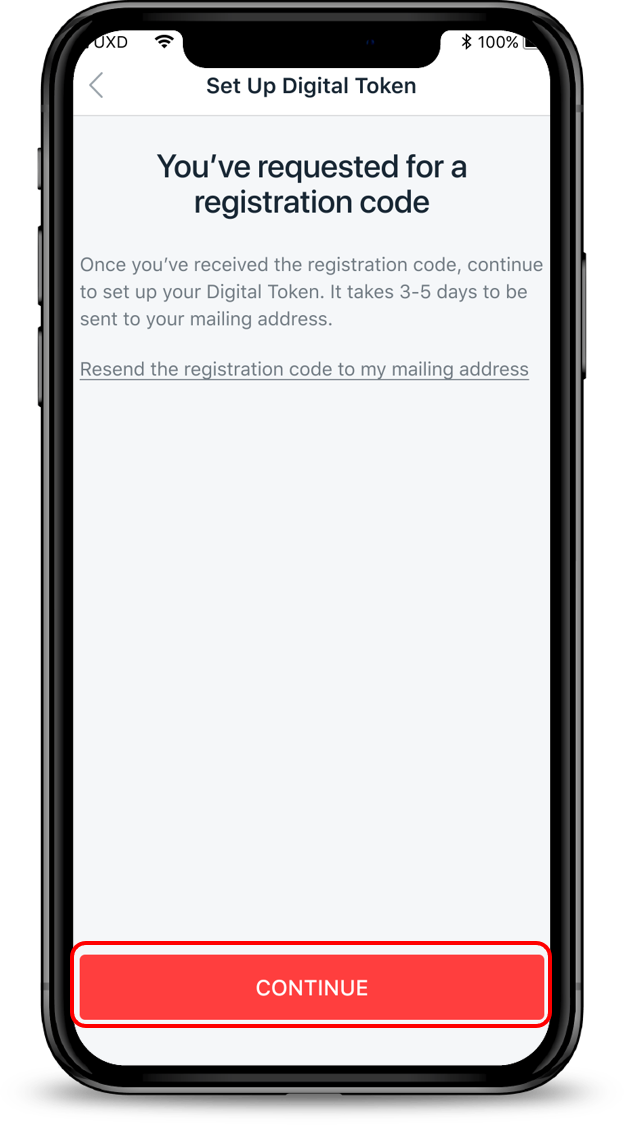 Source: dbs.com.sg
Source: dbs.com.sg
Order Tokens Directly from Duo. A hardware token eToken. They have their pros and cons. If a user forgets their phone or hardware token but still needs access. Hard tokens are physical objects used to grant access to a restricted digital asset.
 Source: dbs.com.sg
Source: dbs.com.sg
To do so you must. Both tokens generate a single-use code to use when accessing a platform. Order Tokens Directly from Duo. Soft tokens replace the physical hard token with a software application that can run on a variety of devices. A token is a device that employs an encrypted key for which the encryption algorithmthe method of generating an encrypted passwordis known to a networks authentication server.
 Source: protectimus.com
Source: protectimus.com
Token based authentication systems are stronger more secure because they require two-factor authentication. There are three basic categories of hardware authentication tokens on the marketvisual tokens which display a code to be entered touch or plug-in tokens which enter codes or credentials themselves via USB and wireless tokens which enter codes or credentials over the air using near-field communication NFC or low energy Bluetooth BLE. A hardware token eToken. The hard token vs soft token question is actually pretty straightforward. When I was checking them the vendor listed the SKUs with battery life listed in years.
 Source: doubleoctopus.com
Source: doubleoctopus.com
Hard tokens Hardware token Hard Token are physical devices used to gain access to an electronically restricted resource. Soft tokens Software token Soft token are just that. Import hardware tokens to AuthPoint. Software tokens do have some significant advantages over their hardware-based counterparts for both organizations and end users. The software tokens can be installed on a users desktop system in the cellular phone or on the smart phone.

There is no sense to dispute this fact but it must be kept in mind that it is worth it. Duo supports third-party hardware tokens like Yubicos YubiKeys or any OATH HOTP-compatible tokens. Token based authentication systems are stronger more secure because they require two-factor authentication. For example you cant lose a software-based token feed it to the dog or put it through the wash. Duos D-100 tokens have an expected minimum battery lifetime of 2 years.
 Source: pinterest.com
Source: pinterest.com
In other words with a token based system the user must provide a PIN AND the output from the token. There are three basic categories of hardware authentication tokens on the marketvisual tokens which display a code to be entered touch or plug-in tokens which enter codes or credentials themselves via USB and wireless tokens which enter codes or credentials over the air using near-field communication NFC or low energy Bluetooth BLE. Both tokens generate a single-use code to use when accessing a platform. Duo supports third-party hardware tokens like Yubicos YubiKeys or any OATH HOTP-compatible tokens. A hardware token eToken.
 Source: pinterest.com
Source: pinterest.com
As the MobilePASS software token is installed on your smart phone you are less likely to lose the token a common issue with hardware tokens Unlike hardware tokens MobilePASS software tokens never expire so there is no need for periodic replacements. Hardware tokens are popular for IT admins that want to have a more physical management of keys. In other words with a token based system the user must provide a PIN AND the output from the token. The factors in a token based system are something the user knows a PIN and something a user has the token. They are only available in increments of 10.
 Source: posb.com.sg
Source: posb.com.sg
But soft tokens are pieces of software which makes them intangible. For example you cant lose a software-based token feed it to the dog or put it through the wash. There is no sense to dispute this fact but it must be kept in mind that it is worth it. Duo supports third-party hardware tokens like Yubicos YubiKeys or any OATH HOTP-compatible tokens. There are hardware MFA such as RSA tokens that generate codes.
This site is an open community for users to do submittion their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site helpful, please support us by sharing this posts to your preference social media accounts like Facebook, Instagram and so on or you can also bookmark this blog page with the title software token vs hardware token by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.





